Unfortunately, there is no easy button on this one. Migrating to new hardware model of Firepower Management Center (FMC) is a manual and very time-consuming process so my goal is to highlight the steps I had to go through as I’ve converted to different hardware model due to IPS limitation.
First, connect new FMC to your network and go through the initial setup process. By default FMC NIC is set for DHCP so as long as access Vlan is DHCP enabled FMC will pull IP address. Once in the GUI go to System > Configuration > Console Configuration and setup CIMC.
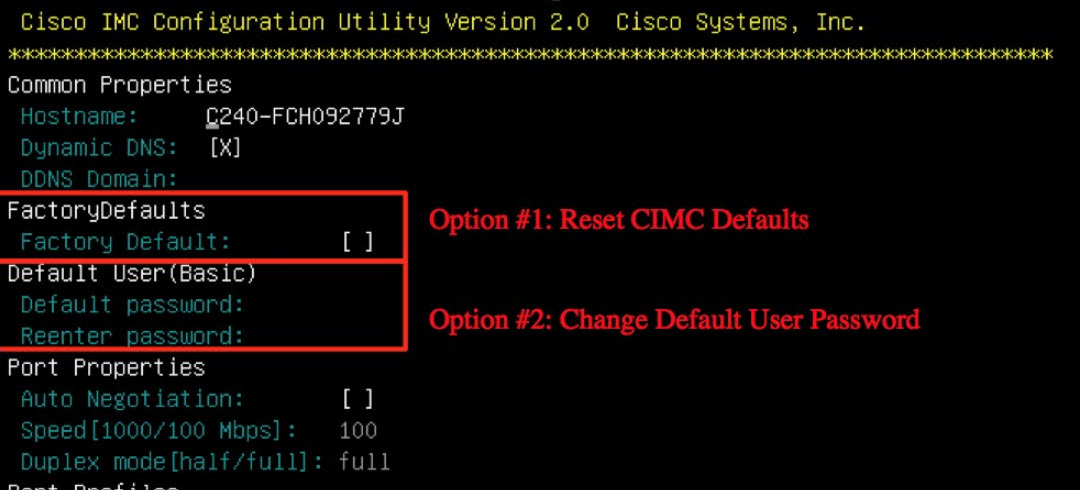
When IP is set do test connectivity to CIMC. I had major problems with the default password. Neither “password”, “Admin1234”, “Cisco1234” worked so I’d to perform CIMC Factory reset. You can still do it when remote but you will have to switch to console mode and reboot is required.
Next, install matching software/rule updates on new FMC. If production FMC updates are older you will need to download older updates from Cisco and roll back to it. Go to Help > About and make sure all the settings are identical otherwise policy import will not work.
There is no backup/restore between different versions of hardware however you can export/import Access Policy which includes most of the settings you need.
FMC version has to match in order to import Access Policy settings.
On import, most likely you will get a warning message.
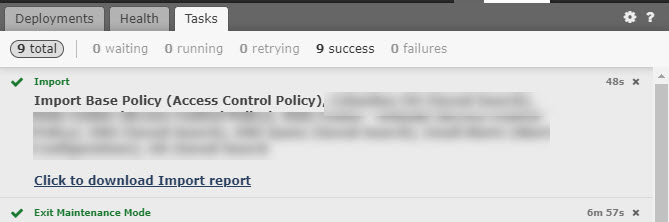
You can try correcting the errors. For example, I was missing some security zones so I’ve created them manually under Objects and tried another import. However, it does not appear to be possible to get rid of all the errors completely as there always be overlapping instances so proceed with import and generate Import Report. It will help you identify duplicate entries.
My report identified duplicate Prefilter Policy, Global-Whitelist, Global-Blacklist-for-URL, Global-Whitelist-for-URL, Global-Blacklist.
Update Prefilter Policy under each Access Policy. Unless you’ve modified yours I usually switch it back to default.
Global Whitelist/Blacklist URL and IP lists will have _1 appended. It will retain custom entries from current production appliance.
Since any new entries will be going into new default Global-Blacklist and Global -Whitelist and you can not update it with your current contents. So I’ve just added default lists in addition to Security Intelligence policy. Same goes for URL Whitelist/Blacklist.
The following settings were also imported successfully.
-
- Update schedules for Rules and GeoLocation will be imported.
- Health Policy will be imported. You can remove the initial one and reassing devices.
- All policies and zones under Access Control will be imported.
- with zones, I would rename them. For example, inside to inside1 and I’ll explain the reason later.
After Policy Import check System > Configuration. Most if not all of the items need to be updated so set old and new FMC side by side and copy settings over. The following items I had to update manually.
-
- Login Banner
- Email Notification
- HTTPS certificate
- SNMP
In addition the following items I had to recreate for my particular case.
-
- I had to add Users and re-enable External Authentication.
- Backup/Restore remote storage settings will have to be reconfigured manually.
- Scheduling and installing the latest OS updates will have to be configured manually.
- Device Groups had to be recreated and devices added to them.
Before configuring Integration option install sensor licenses. In order to do that you will have to migrate them from original FMC. It is a manual and tedious process for classic licenses so If you have many then open TAC case and they will do it for you. Licenses will come in over email in batches of 10.
Once licenses installed go to Integration and configure
-
- Cisco CSI
- Identity Sources
Once FMC is fully configured it is time to start moving sensors over to new appliance. Sensors will have to be deleted from current production, new FMC registration information applied through CLI and then manually joined to new FMC. After sensor has been de-registered from production FMC you may run into error on CLI when you try to apply new settings.
Manager Transition in Progress, try again later.
I’ve tried waiting for this error to clear but to speed up the process I just rebooted the sensor with CLI “system reboot” command. Once the sensor is back up it usually takes new setting without any issues.
When you eventually join sensor to new FMC I found there is an issue where the sensor would retain some settings from older FMC which in turn creates conflicts specifically related to interface zones in my case. What I noticed is sensor would show up with zones already assigned but they would not be recognized by new FMC.
So this is when we use our renamed zones and reassign interfaces to them. For example original zone inside – new zone inside1.
Edit and change to new zone.
Once all production sensors are migrated you can rename zones back to their original names.
One last issue I had was with my custom remediation rule. For now I’ve it disabled but will update this post once it is resolved.








2 comments On Cisco FMC: Migration to new hardware
Now version 6.5 gives ability to model migration but if you are on previous version then bets of luck…I am also doing this these days and will send you my model migration document once completed. I am going from 3500 FMC to 4500 FMC in HA on 6.2.3.9-54. Too tedious!!!
Yes I’ve heard about 6.5. Will see how well it does it. I’ll be happy to a add your migration document here to help others with this task.