When someone is running malicious activity against your public facing services just a few high priority alerts is enough to know that source is not trusted and there is no need for them to keep wasting your IPS cycles. Ideally, it would be to have correlated remediation action automatically adding offenders to the blacklist.
Components:
Firepower Management Center: 6.2.0.2
By default, this action is not available but fortunately, a custom script is created and available at Cisco Support Community forum.
Note this is not supported by TAC and any actions you take by deploying this script is at your own risk.
Author comments and PDF instructions are very informative so I’ll just enhance it with my findings and some of the missing pieces that can help you with deployment of this module.
First, create new Network feed where malicious IP will be recorded. This will be referenced in your Security Policy Blacklist section. Create new feed under Objects > Object Management > Network Lists and Feeds > Add Network List and Feeds.
Give it a name and populate the following values. Feed URL means feed will reside locally on FirePOWER Management Center (FMC) and MD5 hash will be used to verify for errors. Click Save.
Now we need to associate new feed with Access Control Policy under Policies > Access Control > edit Policy > Security Intelligence tab. Select your feed under Networks and add it to Blacklist section.
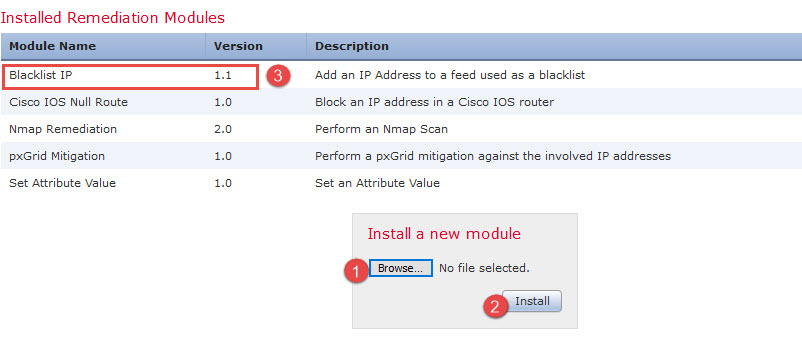
Next, download custom remediation installation package and unzip it. At the time of this writing version 1.1 was the latest one.
Upload new module to FMC under Policies > Action > Modules
Install only works on 6.2 and prior. Newer versions return “not a valid module file” error. However if installed on 6.2 and upgraded it appears to function normally.
Next, create new Instance within this module under Policies > Action > Instances.
The module can have multiple instances, one per device.
After an instance is created edit it to add new Remediation Action. In my case it is Blacklist Source IP.
In remediation action properties specify Network Feed filename defined earlier. As a number of maximum entries reached older IPs will be purged but this option can be disabled.
Now you should see new Remediation Action created. Save it and go to the next step.
Go to Policies > Correlation > Rule Management > Create Rule. Specify events to trigger this rule. In addition setup connection tracker to execute this rule only after so many repeated events.
Correlation Rule by itself is very straightforward but keep in mind the following.
- It is definitely a good idea to start with connections initiated outside of US and define outside as Ingress interface.
- After some testing, I had to exclude Private subnets from this rule. This would be the case of full tunnel VPN clients which were flagged as Unknown Country (due to private IP range) and connecting on outside interface.
On version 6.2 I had issues with complex conditions not working so if you need to create one you will need to create multiple rules.This turned out to be a misconfiguration on my part. With (not in) need to use logical “and” (&). I’ve updated screenshot with correct logic.- Added Reason condition matching IPS Block to skip connections already blocked by Access Control rule.
Next step is to create Correlation Policy under Policies > Correlation > Policy Management
Select Create Policy, give it a name and Add Rules. Add the rule you just created.
Once added scroll all the way to the right and select Responses.
From the list of Unassigned Responses select the one you just created and select Update. In addition you can add email alert to be notified when rule is triggered.
Finally on the Correlation Policy page enable new policy.
Lets see this rule in action. Two malicious events come in outside of US. They were triggered by IPS signature and were bocked.
When third event comes in Correlation Event is triggered.
And source IP is added to Blacklist feed located under /var/sf/htdocs/.
To remove IP from your custom Blacklist feed you need to simply edit custom_blacklist.html file with vi editor (need to be root) and do not forget to update MD5 hash file with this md5sum command:
sudo “md5sum /var/sf/htdocs/custom_blacklist.html > /var/sf/htdocs/custom_blacklist_md5.html”
This module has been running great for the last few weeks. Once tweaked and tested it makes perfect addition to network security perimeter architecture.

















9 comments On FirePOWER: Custom remediation action
I am attempted to use this module, but for an specific rule 45304 web logic. I want to block the source in since it continues running scans.
Have you tried adding “Rule SID is 45304” condition with logical AND?
yes I did. Found out I had the old tar.gz 1.0. So I remove it and replaced with the updated tar.gz 1.1
It worked! Thanks a lot
I couldn’t get it to work with FMC 6.3
I have not done it on 6.3. Once I do I’ll update.
Somebody should give you a NOBEL !
Dear Admin, if it possible please don’t forget to modify this script for FMC 6.4, I will be appreciate you.
Today I have tested, it is working on FMC 6.4 !!!