When you start Cisco Identity Services Engine (ISE) BYOD deployment you will realize a need for a flexible reporting tool and ISE reports will not be enough. For example, if you need to run reports by wireless location, or by EAP authentication method, or to distinguish between certificates deployed by ISE SCEP or Microsoft GPO. Splunk works great for that but before you start, make sure you are parsing ISE data correctly as discussed here.
Components:
Cisco ISE: 2.0
Splunk: 6.2.3
Most likely you start your wireless BYOD deployment one site at a time and will need some way to distinguish those locations when you start enforcing BYOD and running reports. Device groups concept does not work well with WLC deployment where a single controller controls geographically diverse AP’s.
One workaround is to name AP by location, for example, orl-ap01, where orl stands for Orlando in this case and then change Auth Called Station ID Type on WLC under Security tab to AP Name.
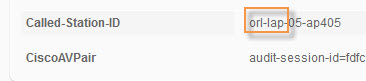
Now, if we look at ISE Radius Live Log > Detailed Authentication Report Called-Station-ID value identifies site location and we can use it in ISE as a site enforcement criteria and later in the Splunk for reports.
In ISE under Policy > Policy Elements > Conditions > Authorization > Compound Conditions create new condition. The compound condition will include Radius: Called-Station-ID as defined above. In our example it is orl.
Next, add a rule to Authorization Policy and reference new condition. Assuming all other policies for BYOD process were configured correctly when people from Orlando login with PEAP credentials they will be forwarded to BYOD process but the rest will continue to login normally. By gradually adding sites to this new condition you can manage and address any first-day support issues and achieve successful BYOD migration.
Now in order to understand what is happening at the site you need a powerful reporting engine. Splunk has Cisco Security Suite App with Identity Services Add-on. What we need to do is tweak it a bit.
First, I’ve created a lookup file called ISE_mylocations.csv so I do not have to memorize site location codes and have a very convenient drop-down menu. This file should be placed in the location indicated below and have rw privileges for root.
To populate this file with new data we need to add lookup config to savedsearches.conf file. This Lookup table will be updated every 24 hours so when a new site is added it will be refreshed automatically. I’ve copied and modified existing file to /local folder so new app updates do not overwrite it.
Additional code I’ve added is below.
[Lookup – myLocations]
action.email.inline = 1
alert.suppress = 0
alert.track = 0
cron_schedule = 0 * * * *
description = Updates the ISE_myLocations.csv lookup file created by *FINKOTEK*
dispatch.earliest_time = -24h@h
dispatch.latest_time = now
enableSched = 1
run_on_startup = true
search = eventtype=”cisco-ise” Called_Station_ID=”*” | rex field=Called_Station_ID “(?P<mylocation>\w{3}).*” | stats count by mylocation | inputlookup append=T ISE_myLocations.csv | stats count by mylocation | table mylocation | outputlookup ISE_myLocations.csv
Now we need to reference this data in Identity Services tab. On this tab Select Edit > Edit Panels > Add Input > Dropdown.
Provide Label and Token to be used in your custom queries. Label can be arbitrary but Token has to match selected variable (highlighted in red above). In our case, it is mylocation.
Scroll down and add Dynamic Options. Match dynamic fields with the same value to keep it simple. Apply when done.
When lookup script runs it will populate csv file which will populate the drop-down menu.
Now let’s edit one of our custom queries and add reference to the dropdown label. Below query will produce all profiled endpoints at the selected location.
eventtype=cisco-ise Called_Station_ID=”$mylocation$*” NAS_Port_Type=”Wireless – IEEE 802.11″ | stats dc(user) as count by EndPointMatchedProfile | sort -count | `format_field_names`
When we run this query we will get only devices associated to AP’s at this location.
 Below are a few more queries I found useful during BYOD deployment.
Below are a few more queries I found useful during BYOD deployment.
All Devices by Authentication Method
eventtype=cisco-ise log_type=Passed_Authentications Called_Station_ID=”$mylocation$*” NAS_Port_Type=”Wireless – IEEE 802.11″ | stats dc(user) as UserCount by AuthenticationMethod | sort -UserCount
All Devices by Authorization Policy
eventtype=cisco-ise log_type=Passed_Authentications Called_Station_ID=”$mylocation$*” NAS_Port_Type=”Wireless – IEEE 802.11″ | stats dc(Name) as UserCount by AuthorizationPolicyMatchedRule | sort -UserCount | `format_field_names`
The newer versions of ISE will eventually contain contextual improvements on the reporting side but the best part about Splunk will be it’s flexibility when queries can be customized and tuned easily to achieve desired results.