I’ve worked before with RSA Multi-Factor Authentication (MFA) solution but this is the first time I’ve integrated cloud-based MFA. I’ll skip configuration related to DUO setup and will concentrate on what is relevant to Cisco. With all kinds of DUO configuration guides and whitepapers I’ve struggled to find a clear guide for most common Cisco setup: Anyconnect VPN > ASA > ISE. As a result, I started all wrong with adding DUO as Radius Token to ISE. My assumed authentication flow looked similar to the diagram below.
With this approach I was getting strange errors such as MSCHAPv2 protocol not supported by DUO authentication proxy and logins were rejected.
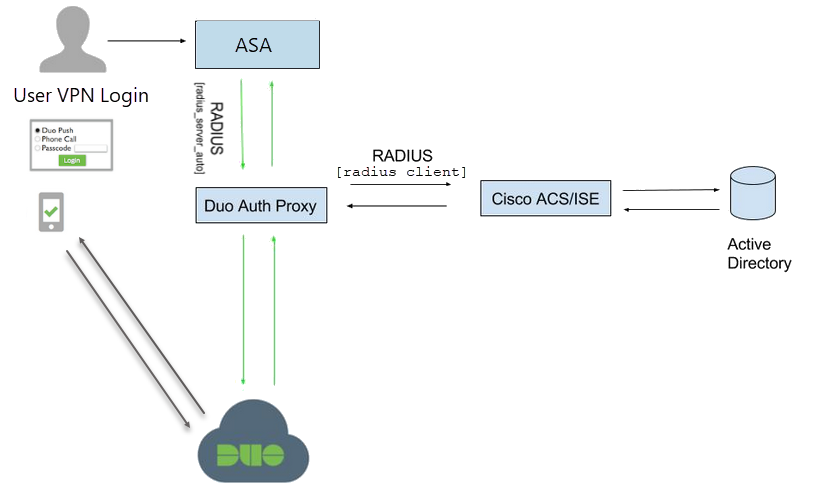
The proper Another way to integrate DUO in the production network is depicted below. As you can see all authentication requests from Cisco ASA go to DUO proxy authentication servers (Proxy) then DUO has ISE servers configured as Radius clients which in turn authenticates users against Active Directory. Authentication result with any additional attributes is passed back to DUO which in turn initiates MFA process (push, code, etc). This setup also allows us to introduce DUO to existing production without any major configuration changes.
Start with DUO configuration. On DUO Admin page navigate to Groups and add test Group of users who will be enrolled in preliminary testing of MFA.
Next, go to Applications > Protect an Application.
Search for Cisco Radius VPN app to process authentication requests from ASA. Select Protect this Application to install.
Once installed make note of Integration key and Secret key
Scroll down and Edit Global Policy.
Select Allow access without 2FA to insert MFA into the existing authentication flow and let users authenticate if MFA token is not assigned. 
Save changes, scroll down and enable Username normalization so usernames with appended or pre-pended domain names are not bypassed or denied.
Optionally select you test user group to allow authentications from. Save changes.
Save changes.
Next, login to DUO Proxy server and edit config file located at C:\Program Files (x86)\Duo Security Authentication Proxy\conf\authproxy.cfg.
Add radius_client section with IP addresses of Cisco ISE PSN servers.
[radius_client]
host=ISE1_PSN_IP
host_2=ISE2_PSN_IP
secret=Radius_secret_key
If you plan on passing Radius Attributes from ISE back to ASA through DUO do not forget to enable these options otherwise it will be blocked by DUO. For example, for Group Policy enforcement allow this attribute.
pass_through_attr_names=Class
To allow passing all attributes:
pass_through_all=true
Edit radius_server_auto section. Add Cisco Radius VPN app keys and API hostname. Also, specify ASA IP address and Radius secret. Attribute pass_through_all=true allows passing Radius attributes to ASA from ISE. With attribute failmode=safe If Duo service is unreachable, users will be ALLOWED access if they pass primary authentication.
[radius_server_auto]
; Your Duo integration key
ikey=App key
; Your Duo secret key
skey=App key
; Your Duo API hostname (e.g. “api-XXXX.duosecurity.com”)
api_host=api-xxx
radius_ip_1=ASA_IP
radius_secret_1=Radius_secret_key
client=radius_client
failmode=safe
pass_through_all=true
port=1812
Once configuration changes were made restart DUO service from Admin mode command line.
net stop DuoAuthProxy
net start DuoAuthProxy
Make sure service starts successfully, if not check the log file for errors (C:\Program Files (x86)\Duo Security Authentication Proxy\log).
Next, configure the Cisco ASA with DUO Proxy servers. Very important to have at least two DUO servers for redundancy and set timeout to 60 seconds.
aaa-server DUO-MFA protocol radius
aaa-server DUO-MFA (inside) host DUO_Proxy1_IP
timeout 60
key *****
authentication-port 1812
accounting-port 1813
no mschapv2-capable
aaa-server DUO-MFA (inside) host DUO_Proxy2_IP
timeout 60
key *****
authentication-port 1812
accounting-port 1813
no mschapv2-capable
In case you start experiencing timeout issues during authentication prompt check this post about timeout values configured on Anyconnect XML profile.
Add DUO server group to Anyconnect tunnel group as the authentication server.
tunnel-group AnyConnect-Group general-attributes
authentication-server-group DUO-MFA
Next, on Cisco ISE add DUO Proxy servers to the device group. Use the same Radius secret as on DUO Proxy config.
Create Authentication Identity sequence to authenticate VPN users to identity source.
Create Allowed Protocols profile for VPN authentications. Allow only PAP/ASCII.
Configure the new Authentication Policy Set for VPN authentications. Select DUO device group as Condition. That way your existing authentication flow is not impacted.
Configure authentication policy to use configured VPN sequence.
Create Authorization policy. Optionally specify conditional attributes to selectively apply authorization results. For example, I used Dial-in attribute so I can control who can VPN in while in MFA bypass mode.
That it. If the user is not part of test group they will bypass MFA. As for your test users and future production, deployment follow DUO Liftoff Guide for best user experience.
Update.
As I learn more about DUO I came across Radius-Challenge option. Unfortunately, I did not implement it yet and there are no screenshots with Anyconnect so, for now, Global Protect will do. More information can be found here but this is a great option for self-enrolling users like new hires. The only part I do not like is that you can not be specific on what to display. For example, I want this challenge to only pop up for self-enrolling users and for enrolled users send straight push notification without extra pop-ups but unfortunately it is not possible. Maybe future releases will have more flexibility.















17 comments On DUO MFA with Cisco Anyconnect and ISE
Why could you not get this to work with Duo Proxies as RADIUS Tokens? I have this working currently. The ASA looks to ISE, and then ISE looks to DUO Proxy, Proxies auth to DUO cloud and AD and then send back to ISE then back to ASA. The only issue I am having is the timing values with timeouts. Sometimes I get strange things like 3 pushes in a row real fast and it locks the user out. Other then that its working. I have the IPs of ISE in the [radius_server_auto] field and I do not sue the radius client field at all.
Steven, I was getting MSCHAPv2 protocol not supported by DUO error in ISE logs. And working with DUO support we found this design the most efficient. Also additional features such as Radius Challenge can be enabled directly on DUO (I’m not sure if ISE was inline this is possible). I’m also not seeing any issues with timing or duplicate pushes.
Ok, now thats what I am seeing is timing issues and multiple pushes for one auth and essentially locks the user out, which becomes frustrating to users and my help desk. I have also come across the fact that if a user is NOT enrolled in DUO at all or their username is incorrect in DUO, that they can freely login with username and password with no DUO push, I assume this is because as soon as the ASA verifies AD association of the user it hands that back to the ASA without waiting for DUO verification. I have been on support with DUO for weeks now and I have told them about this article and was upset that before this article they were not steering me the right way in the design.
I am still struggling with this deployment and DUO has been very little help. Is there a better method of contact for you that posting here? I have a few more challenges than this article with help with and I am just missing some info I can’t seem to find here with your limited screen shots.
I have reworked the traffic flow. I am not sure if you are using dACLs or not in this example, but I have some issues with that. What are your timing values for the anyconnect client? I have the Duo servers set to 60 seconds and the anyconnect client for 60 seconds as well using the xml profile. The DUO pushes are very delayed which then causes the user to be locked out. Any other tips?
No dACLs or any Radius options in my setup. 60 sec on Anyconnect and no timeout set on DUO Radius_client or Radius_server. Have you tried removing dACLs and any other option and just use plain authentication?
I have not, but it won’t be an option as the dACLs are mandated by corporate security. I am reading what needs to be done is that the ASA needs to use Duo for authentication and ISE for authorization. So I need to set these up separately in the anyconnect connection profile. I can only assume that when the asa passes CoA to DUO on port 1700, Duo Proxy doesnt know what to do with it so it drops it.
On Anyconnect XML profile make sure Primary Server FQDN matches your ASA FQDN.
Splitting auth and authz may be the way to go. I do not have it in my setup. But that again introduces more complexity. If I were you I’d start simple. May be even spin up a test asa where there are no mandated restrictions and at least rule out basic setup with plain auth. Then if all is well move into split auth/authz configuration testing.
Very good guide! Do you know if is there a way to failover from push notification to token? I like using the push but if I’m in a location where my phone doesn’t have coverage I need to use the token and I’m struggling to configure this. Have you ever came across this?
Thanks in advance,
Albert
You can append it to password – “password,passcode”
https://guide.duo.com/append-mode
Has anyone figured out how to get CoA dACL back to the ASA via DUO.
Currently the DUO log sees this dACL as another user authentication attempt with the dACL name as the user name.
VPN connect if I don’t use dACL, but this is a requirement.
Great post! Out current deployment is the same and works like a charm. But i saw you are preparing post “ DUO MFA with Cisco Anyconnect and password change”, do you have any progress with it?
Hi, will have it done in a few days. Thanks
Highly appreciate your work for this! Thank you!
Good luck trying to get this to work with dacl
You are right. For dacls it has to change . We do loose some DUO functionality but it is a working solution.