In continuation to my previous post about DUO and ISE integration, I came to a problem where I had to integrate ISE posture into the mix. Passing standard Radius attributes with the existing setup was not an issue but since posture required a bit more complicated authentication flow it did not work. I was getting the following error:
The source of CoA packet does not match tunnel-group config.
CoA message from xxxx for session ac1463040011a0005df838de is inconsistent with the ASA configuration.
My setup was as below so the response from ISE obviously did not match actual Radius server configuration on the tunnel-group.
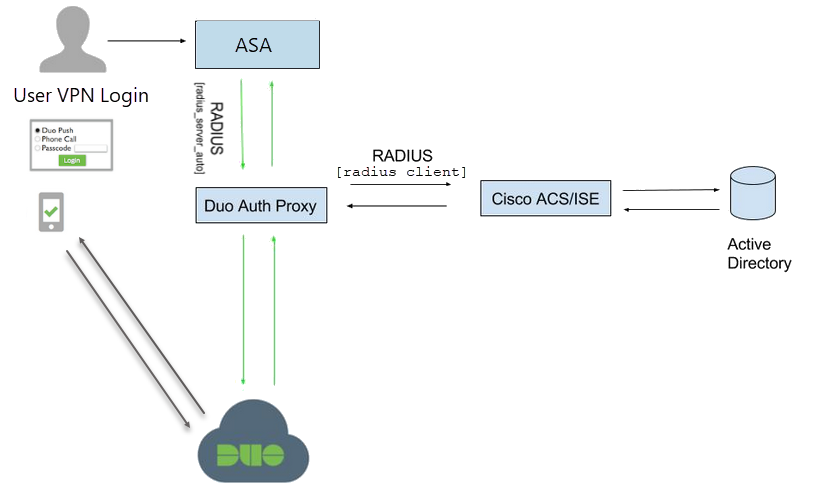
So I had to revert it to the original diagram below.

As you can see all authentication requests that are properly formatted (push, code, etc) from Cisco ASA go to Cisco ISE servers. Then ISE has DUO servers configured as external Radius servers which in turn authenticate users against Active Directory. Authentication result is passed back to ISE on success initiating the Posture process.
With this setup, there are no additional menus to assist users. User has to be educated on proper password field format to successfully authenticate.
Start with the DUO configuration and complete it based on the information provided.
Next, login to DUO Proxy server and edit config file located at C:\Program Files (x86)\Duo Security Authentication Proxy\conf\authproxy.cfg.
Edit ad_client section. Add host as IP of Active Directory Servers. Add host_2 for redundancy. Specify service account username and password for AD query and base search DN.
[ad_client]
;Active directory server IPs
host=AD1_IP
host_2=AD2_IP
;AD account to run queries.
service_account_username=username
service_account_password=password
search_dn=DC=company,DC=local
Edit radius_server_auto section. Add Cisco Radius VPN app keys and API hostname. Also, specify IP addresses of Cisco ISE PSN servers and Radius secret. With attribute failmode=safe If Duo service is unreachable, users will be ALLOWED access if they pass primary authentication.
[radius_server_auto]
; Your Duo integration key
ikey=App key
; Your Duo secret key
skey=App key
; Your Duo API hostname (e.g. “api-XXXX.duosecurity.com”)
api_host=api-xxx
radius_ip_1=ISE_IP
radius_secret_1=Radius_secret_key
client=ad_client
failmode=safe
port=1812
Once configuration changes were made restart DUO service from Admin mode command line.
net stop DuoAuthProxy
net start DuoAuthProxy
Make sure service starts successfully, if not check the log file for errors (C:\Program Files (x86)\Duo Security Authentication Proxy\log).

Next, configure the Cisco ASA with ISE servers. Very important to have at least two ISE servers for redundancy and set timeout to 60 seconds.
aaa-server ISE protocol radius
authorize-only
interim-accounting-update periodic 1
dynamic-authorization
aaa-server ISE (inside) host ISE1_IP
timeout 60
key *****
aaa-server ISE (inside) host ISE2_IP
timeout 60
key *****
Add ISE server group to Anyconnect tunnel group as the authentication server.
tunnel-group DefaultWEBVPNGroup general-attributes
authentication-server-group ISE
I found accounting not necessary in this configuration
Next, on Cisco ISE add External RADIUS Servers. Use the same Radius secret as on DUO Proxy config for radius_secret.

Make sure and set Server Timeout to higher than ASA timeout. In our case 65 seconds as noted here.
Create RADIUS Server Sequence to authenticate VPN users. Add Radius servers to the sequence.

Under Advance is very important to check Continue to Authorization Policy otherwise ISE Authorization will not take place.
Configure a new Authentication Policy Set for VPN authentications. Select RADIUS Server Sequence. You can split your test VPN device into a separate group. That way you will not impact production.

Create an Authorization policy based on posture assessment requirements by following Cisco guides.
Unfortunately with this setup, we lose user-friendly pop-ups from DUO proxy. Anyconnect login screen will have the usual username/password fields. Un-enrolled users will still be able to VPN in. Enrolled users will have to append coma and keyword (push, SMS, etc) to their password and reenter it again once they get the code or look for a pop-up on their phone as it is the default action.
If you start seeing USERNAME instead of real user id for failed attempts check this setting under ISE 2.4 – “Disclose invalid usernames”. If it is unchecked then check it.
With upgrade to 2.6 this option will reset so you will start seeing USERNAME again. Go to Settings below and check it back. Make sure to apply all the latest patches if you can not save your changes.


