Another addition to posting about DUO and ISE integration. This time it is about password change.
After researching various option I came across the following 3 solutions.
1. Add a dedicated connection profile, call it Password_Reset and authenticate users directly to LDAP or ISE. This works OK for this setup and when you already have a drop-down on Anyconnect so there is nothing new to the end-user other than original options. If you have no drop down and enforce Group Policy through ISE Authorization it may be an issue.
2. Implement SAML. I’ve not done it but seems to be a viable option. Requires additional steps like importing Access Gateway certificate and SSO server setup which adds complexity to configuration and troubleshooting but brings back missing user experience based on screenshots below.
3. Implement a secondary authentication mechanism on Cisco ASA. ISE is the primary authentication source and DUO is secondary. This allows for ISE to process password change requests and once completed use DUO as a second authentication to enforce MFA.
To implement this option you need to be setup with DUO MFA as discussed in this post. The following changes will need to take place.
Login to DUO Proxy server and edit config file located at C:\Program Files (x86)\Duo Security Authentication Proxy\conf\authproxy.cfg.
radius_server_auto section can be removed or left as-is with IP addresses of Cisco ISE PSN servers.
Add new section radius_server_duo_only. Copy ikey, skey, and api_host values from radius_server_auto. For radius_ip use ASA interface ip that is defined on aaa server configuration below.
[radius_server_duo_only]
; Your Duo integration key
ikey=App key
; Your Duo secret key
skey=App key
; Your Duo API hostname (e.g. “api-XXXX.duosecurity.com”)
api_host=api-xxx
failmode=safe
radius_ip_1=ASA_IP1
radius_secret_1=Radius_secret_key
Once configuration changes were made restart DUO service from Admin mode command line.
net stop DuoAuthProxy
net start DuoAuthProxy
Make sure service starts successfully, if not check the log file for errors (C:\Program Files (x86)\Duo Security Authentication Proxy\log).
Configure Cisco ASA with ISE servers. Very important to have at least two ISE servers for redundancy and set timeout to 60 seconds.
aaa-server ISE protocol radius
authorize-only
interim-accounting-update periodic 1
dynamic-authorization
aaa-server ISE (inside) host ISE1_IP
timeout 60
key *****
aaa-server ISE (inside) host ISE2_IP
timeout 60
key *****
Configure Cisco ASA with DUO proxy servers.
aaa-server DUO_MFA protocol radius
aaa-server DUO_MFA (inside) host DUO1_IP
timeout 60
key *****
aaa-server DUO_MFA (inside) host DUO2_IP
timeout 60
key *****
Configure DUO as secondary authentication servers on the default tunnel-group. use-primary-username option removes the secondary username field. You can also modify authentication prompt for the secondary password as explained in this article. password-management option enables support for password change and specifies the number of days before the password expires.
tunnel-group DefaultWEBVPNGroup general-attributes
authentication-server-group ISE
secondary-authentication-server-group DUO_MFA use-primary-username
password-management password-expire-in-days 5
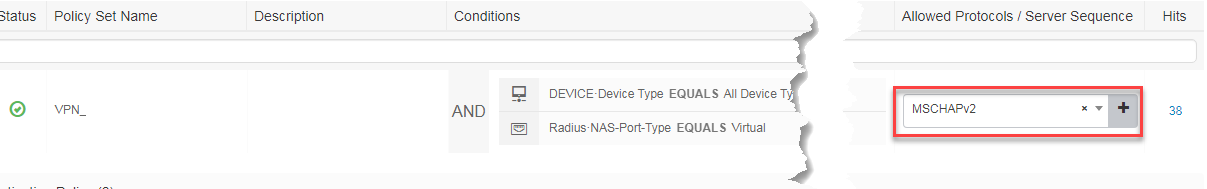
Next, modify Cisco ISE policy configuration. First, under Allowed Protocols change it from Proxy Sequence to Allowed Protocols and make sure MSCHAPv2 is enabled in order to support password change. PAP will not work.
Under Authentication Policy make sure your Primary authentication store is selected (ex. MS AD).
Authorization policies will stay as-is.
If you followed the above instructions your Anyconnect authentication prompt will look like below.
DUO Passcode field will accept keyword “push” or passcode from the DUO app (airplane mode). The passcode will only work once so you will need to renew it for the next login.
Important DUO Passcode: field is global and can not be blank (I’ve read about some Java scripts that can pre-populate this field but did not test it). If you have users who are not enrolled in DUO (in bypass mode) they need to be educated to enter some value.
When password change event takes place user will be prompted to change their password after which authentication will fail. User will have to login again with new password and choice of DUO MFA.
P.S. I just came across another advantage of this setup. User account under which DUO service was running on proxy box got locked out (note: always use service account) and DUO authentication started failing. In previous setup VPN connectivity would fail completely even with failmode=safe option enabled however this setup continued to work because DUO was setup as secondary authentication mechanism.





7 comments On DUO MFA: with Cisco Anyconnect and password change
Hi, thanks for this post! I was able to follow your steps above and have ran into a somewhat complicated issue.
We have a Firepower (FTD) configured for VPN access instead of an ASA, but most of the configuration above is the same. I’m able to authenticate users perfectly fine against AD through ISE and Duo for second factor authentication.
My issues arise the moment I enable password management. It seems as though Duo can’t process MSCHAPv2 requests, which as I understand is how ASA/FTD send authentication requests once password management is enabled. Did you need to do anything extra to allow users to change passwords with Duo as the second factor? If I could send the authentication request to ISE as MSACHAPv2 and to Duo as simple PAP, I’d be golden. Unfortunately I don’t think that’s how configuration on the ASA/FTD works, since the password management option is tied to the tunnel group and not to specific AAA servers.
Any help is much appreciated. All the Duo docs that I’ve read specifically say that MSCHAPv2 is not supported by the Duo authentication proxy, and one of the docs even said specifically not to enable the password management field. Been a real headache for the past couple days.
Thanks again for the guide!
-McN
Hi, DUO does not handle password management. It is setup only to handle secondary authentication. ISE needs to be specifically configured for MSCHAPv2 to accept those requests.
Hi McN, do you solve this issue with FTD??
Thanks
Thank you for the post! Option 3 is the most working solution, unfortunately users must fulfill one more line, but this is acceptable.
All your DUO posts have been of great help!
Is there any option where I could change the password with DUO MFA and use ISE Posture in the same time. Do you think this diagram can do it:
Anyconnect → ASA → ISE (posture) → AD (as primary auth)
↘ DUO auth proxy (as secondary auth)
Thank you for your help
This absolutely will work with ISE posture. Give it a try.
Hi, thanks for this post, i was able to implement Cisco DUO as secondary authentication, my primary authentication is Microsoft NPS in witch we have some radius attributes such as Group Policy, Tunnel Group.
Thanks.